Verifying the ownership of a SIM card is an important action in ensuring the safety of your mobile account. When you register for a new wireless service, you'll need to provide identifying information and potentially undergo an authentication process. This helps prevent illegal use of your SIM card and safeguards your data.
SIM card details typically include your specific International Mobile Subscriber Identity (IMSI), customer name, mobile number, network, and issue date. Accessing these details may require contacting your wireless copyright. They can provide you with valid information regarding your SIM card ownership.
- Remember the importance of protecting your SIM card details and avoiding sharing them with unauthorized individuals.
- If you suspect any illegal activity related to your SIM card, immediately contact your service provider.
Viewing Your SIM Information and Rights
Knowing your SIM information can be valuable in controlling usage. This includes details like your unique IMEI number, provider name, and plan type. Furthermore, understanding one's rights concerning SIM cards is crucial for safeguarding control. This means being educated about guidelines regarding data sharing, SIM card blocking, and potential problems that may happen.
Make sure to familiarize yourself with the conditions set by your service provider and stay informed about any changes that may happen. This will empower you to take conscious decisions regarding one's mobile connectivity.
Obtaining SIM Owner Details Securely
Securing personal information is paramount during these digital age. When it comes to accessing SIM owner details, strict adherence to security measures is vital. Verified entities only should request access to this sensitive data by means of established and approved channels.
- Utilize robust authentication protocols to verify the identity of those requesting access.
- Employ encryption techniques to secure sensitive information during transmission and storage.
- Maintain a strict documentation regarding all access attempts, including date, time, and purpose.
- Carry out regular security audits to identify vulnerabilities and strengthen safeguards.
By implementing these practices, we can mitigate the risks associated with accessing SIM owner details and ensure the privacy and security of individuals.
Who Owns This SIM?
In today's increasingly connected world, the question of ownership over our smartphones has become a crucial concern. A key aspect of this discussion revolves around SIM cards, which serve as unique markers for our mobile networks. But who truly owns the information stored on these tiny devices? This is a question that demands transparency and a click here dedication to empowering individuals with knowledge about their cybersecurity.
Unveiling the information behind SIM card control can be a challenging process. Current frameworks often lack the necessary tools to provide users with a clear and thorough understanding of who has access to their SIM card data. However, the growing need for privacy is driving a movement towards greater disclosure.
New technologies are gaining traction that aim to unlock information about SIM card ownership. These include cryptographic protocols, which can strengthen accountability and empower users to have a greater say over their data.
Finally, the pursuit of information transparency in the realm of SIM card ownership is essential for building a secure and accountable digital ecosystem. By promoting greater awareness about who owns our SIMs, we can empower individuals to make smart selections about their digital lives.
Identifying SIM Cards: A Guide to Tracking and Ownership
SIM identification is a crucial process for various reasons, ranging from protection measures to inquiring into illegal activities.
A SIM card acts as the identifier for your mobile device, linking it with a specific phone number and network. Locating a SIM card can provide valuable data about its subscriber.
There are several methods available for determining SIM card ownership, including:
- Authorized requests to mobile network providers.
- Technical analysis of devices and networks.
- Third-party tools that specialize in SIM tracking.
On the other hand, it's important to note that accessing SIM card information demands legitimate authorization and observance with relevant laws and regulations.
Protecting Your Privacy: Managing SIM Card Ownership
Your SIM card acts as a vital component of your mobile access. It houses essential information that identifies you to your service provider. {Therefore|Consequently, it's imperative to maintain control over its ownership.
Keeping a secure SIM card involves several strategies. , Begin by, thoroughly choose your copyright. Explore their standing regarding security procedures.
, Additionally, implement strong passwords for your SIM card. Select a combination of characters that include uppercase and lowercase letters, digits, and special characters to strengthen its security.
{Regularly|Consistently, review and update your SIM card's security options. Stay informed on any vulnerabilities and take steps to prevent them.
Finally, in case of incident involving your SIM card, urgently reach out to your mobile network operator. They can suspend your SIM card and help you regain control of your account.
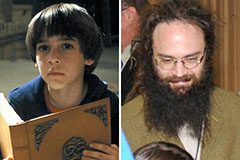 Barret Oliver Then & Now!
Barret Oliver Then & Now!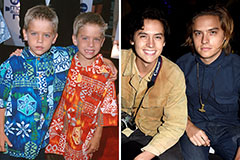 Dylan and Cole Sprouse Then & Now!
Dylan and Cole Sprouse Then & Now!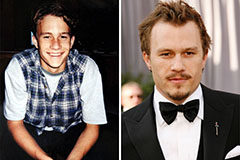 Heath Ledger Then & Now!
Heath Ledger Then & Now! Mike Vitar Then & Now!
Mike Vitar Then & Now! Sydney Simpson Then & Now!
Sydney Simpson Then & Now!